
cherezoff - stock.adobe.com
Russian DDoS hacktivists seen targeting western hospitals
A swathe of attacks by the Putin-supporting DDoS operation known as Killnet has targeted hospitals and other infrastructure in several Nato countries, with the UK thought to be at risk
Healthcare organisations in countries aligned with the defence of Ukraine have been warned they may be at risk of cyber attack by Russian hacktivists after a series of attacks linked to the infamous Killnet group unfolded over the past few days.
Killnet is a hacktivist group of politically motivated actors who have aligned themselves with Putin’s war of aggression. It conducts widespread distributed denial-of-service (DDoS) attacks against targets that have attracted Russia’s ire, and has become infamous since the war began for its campaigns.
It ramped up its attacks again following the decision last week by the governments of Germany and the US to supply Ukraine with tanks, with Germany’s federal cyber security agency, the BSI, reporting incidents at multiple government bodies.
However, in recent days, it seems to have turned its attention to the healthcare sector, institutions for which network disruption, however temporary, could prove highly dangerous.
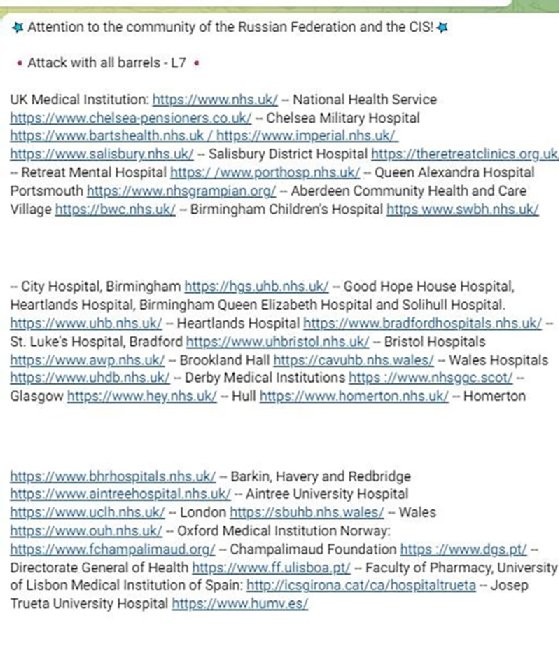
On Monday 30 January, it struck multiple hospital “systems” in the US, but shortly prior to this, a list of potential targets in the healthcare sector, including multiple UK institutions, surfaced online.
The list was shared via Twitter by an independent threat researcher and subsequently shared with Computer Weekly. It names institutions in cities across the UK, including the Royal Hospital Chelsea, a retirement and care home for veterans rather than a hospital involved in frontline NHS care. It also specifies healthcare providers in Germany, the Netherlands, Norway and the US.
Deryck Mitchelson, field CISO at Check Point Software, said: “We know how crippling an attack can be on the NHS. We saw major IT outages last year as a result of a supply chain ransomware attack, much of which continues to have an impact today.
“As more services are delivered online, disruption from DDoS attacks could be even more damaging, potentially affecting emergency care, scheduled appointments and telehealth consultations.
“Although this latest campaign from Killnet is designed to cause disruption for maximum exposure rather than data theft, we should not take these threats lightly. It should be a reminder that we need to prioritise robust security measures in critical services to prevent any further successful breaches,” said Mitchelson.
A warning from cyber history
A DDoS attack, the group’s modus operandi, is a relatively unsophisticated form of cyber attack that floods its targets’ servers, website or network resources with junk messages, connection requests or malformed packets, causing them to slow or crash. They are generally intended more to cause temporary disruption than anything else, and were historically favoured – and still are – by hacktivists, including groups like Anonymous, for precisely this reason.
Indeed, according to Alexander Heid, chief research and development officer at security rating and risk management specialist SecurityScorecard, much of Killnet’s methodology could be said to be inspired by Anonymous.
According to Heid, Killnet has two main attack vectors. Its chief weapon is known as the CC-Attack toolkit, which consists of very few tools and requires limited skills to deploy. It generates three different Layer 7 attack types – Get flood, Head flood and Post flood – which are terms related to the specific requests with which the target infrastructure is deluged.
It also makes use of a tool known as the Low Orbit Ion Cannon (LOIC), a venerable hacking tool popularised by Anonymous, which Heid said was frequently discussed on the encrypted Telegram channel where Killnet organises. Again, it is simple and easy to use, appealing to entry-level threat actors. While easily mitigated, rendering its attacks usually ineffective, the LOIC is still capable of generating a lot of noise.
Prominent supporters
Although it most likely operates at the explicit behest of the Kremlin, Killnet is also known to have some prominent supporters within Russia, according to recent intelligence published by Radware’s head of threat intelligence, Daniel Smith.
In his piece, Exploring Killnet’s social circles, Smith explores how Killnet is attracting support and, crucially, funding. Some of the backers he found included a Russian rapper, Kazhe Oboyma, who released a track last year called Killnet Flow (Anonymous diss).
Smith also explores how it has also garnered support from a company called HooliganZ, a Moscow-based jewellery business, which has produced a line of Killnet-inspired signet rings and has been donating half the profits from its sales of gang merchandise to the operation. This was first reported by Norwegian newspaper Dagbladet.
Meanwhile, the denizens of the Solaris dark web marketplace supposedly clubbed together to have a whip-round for Killnet, according to another report, and donated over $40,000 in bitcoin to the gang.
Read more about distributed denial-of-service attacks linked to Ukraine
- There was a boom in DDoS attacks in the first six months of 2022, according to a report, with Russia’s war on Ukraine helping to drive activity.
- A quarter of cyber security incidents reported to the Financial Conduct Authority in the first six months of 2022 involved DDoS, with a likely link to events in Ukraine.
- A series of DDoS attacks on Ukrainian defence and banking organisations is being firmly attributed to Russian action.









