
sdecoret - stock.adobe.com
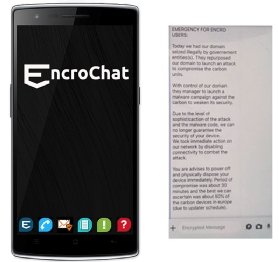
EncroChat lawyers raise questions over use of PII secrecy orders on UK decryption capabilities
Lawyers claim that public interest immunity certificates may have been used to withhold information on UK intelligence agencies’ ability to decrypt encrypted communications
Court hearings into the EncroChat encrypted phone network compromised by the French Police have seen further delays, amid claims that public interest immunity notifications may have been used to withhold information.
Defence lawyers said there was a “broad inference” that public interest immunity (PII) notices had been issued to prevent the disclosure of evidence, which may include information on the UK intelligence agencies’ ability to break encrypted communications.
The National Crime Agency (NCA), working in collaboration with regional organised crime units and other forces, has made more than 1,550 arrests under Operation Ventetic, the UK’s response to the takedown of EncroChat, which police say was entirely used by organised crime groups. The operation has led to the seizure of five tonnes of class A drugs, 155 firearms and £57m in cash.
Under UK law, ministers or prosecutors can apply to withhold information from defence lawyers to protect official secrets, or other sensitive information, on the grounds of public interest immunity, such as the identities of police informers. if its disclosure would be damaging to the public interest.
The crown prosecutors have given no direct response to questions of whether PII notices have been issued. It “must follow that there have been public interest immunity applications without notice for the defence”, one defence lawyer told a court last week.
Defence lawyers are questioning claims by the National Crime Agency (NCA) and the French Gendarmerie that cyber security experts were able to exfiltrate millions of messages using malware planted on tens of thousands of phones before they were encrypted.
The French have refused to disclose how the interception was carried out, citing reasons of “defence security”. The UK courts have accepted evidence from the French investigating officer over the cyber attack as “hearsay” evidence.
“We fail to understand how the prosecution can make such an assertion when one considers that they were relying on hearsay evidence,” and had not conducted a thorough review of whether or not it is a safe assertion to make, one lawyer told a court.
Some experts are understood to have put forward the alternative theory that the French forensic specialists may have decrypted the messages as they passed through a server in the OVH datacentre in Roubaix.
Jonathan Kinnear QC, who is overseeing the national strategy for 250 prosecution cases in the UK, told a judge that that crown would always take a “neither confirm nor deny” position on public interest immunity.
He said that while the defence team were entitled to draw whatever inference he wanted, but they should be careful because it may or may not be right.
Defence lawyers first raised new questions about the capabilities of law enforcement to decrypt live communications after Belgian and Dutch police announced they had infiltrated a second secure cryptophone network, Sky ECC.
Belgian and Dutch police told a press conference on 10 March 2021 that they had intercepted more than one billion encrypted messages from the Sky ECC cryptophone network, and had decrypted half of them.
Defence lawyers said prosecutors had performed “a complete about-turn” from suggesting there was nothing to disclose to applying for an adjournment to review disclosures made to lawyers representing clients in EncroChat cases.
“The only reason for this would be that the prosecution, or at least the prosecuting counsel, did not have sufficient confidence in the answers that have been given 48 hours before, which speaks volumes about the state of disclosure in this case,” said a lawyer representing people charged with offences under Operation Venetic.
He said it was lamentable, given the number of cases impacted by Operation Venetic, that a review of the evidence was taking place at this late stage.
“Any blame for that cannot be laid at the door of the defence for raising an obvious request about the ability of crown agencies to decrypt material,” he told a court.
Kinnear said prosecutors had not begun the disclosure review as a result of any one, single request by the defence. Disclosure was a continuous, iterative process, he said.
He said that the defence case had developed since hearings commenced and in ways that were not set out in the skeleton argument, which he said was “a very bland document putting the crown to proof on the issues of storage and encryption”.
The crown was taking “all matters into account”, and Kinnear said he had a personal obligation as prosecuting counsel to ensure that the disclosure exercise is completed properly “and that is what we intend to do”.
“It is an iterative process. We never profess, in the shoes that I am in now, that we get things right first time, every time,” said Kinnear. “We are conducting a review which I consider is commensurate to the seriousness of the case and the obligations that the Crown owe to each one of the defendants in this case,” he said.
Defence experts disagree over how the French Gendarmerie obtained the decrypted messages, notes and photographs from tens of thousands of phones on the EncroChat network.

The French have refused to disclose how the “implant”, which was procured by the French DGSI internal intelligence agency worked, citing “defence security”.
The US National Security Agency (NSA) and the UK’s GCHQ have developed capabilities to break the encryption used by webmail, encrypted chat, encrypted voice over IP (VoIP), virtual private networks (VPNs) and the encryption used by 4G mobile phone services, classified documents leaked by the NSA whistleblower Edward Snowden in 2013 reveal.
The NSA has also compromised at least one random number generator used as the basis of encryption techniques used in secure communications systems.
A judgment by the Court of Appeal on 5 February 2021, however, found that French police had been able to use a software implant to access messages from phone handsets before they had been encrypted. They were automatically forwarded to a server set up by the French digital crime unit, C3N.
The courts are preparing to hear up to a dozen preparatory hearings that will decide on the lawfulness, admissibility and reliability of material retrieved from the EncroChat network – the decisions in which will be binding on future prosecutions.
The case is expected to resume in May.
Read more about the EncroChat case
- Cops take out encrypted comms to disrupt organised crime: In July 2020, after French and Dutch authorities had gained access to the encrypted EncroChat network, the NCA and its counterparts worked to disrupt the serious and organised criminal networks using the platform.
- Appeal court finds ‘digital phone tapping’ admissible in criminal trials: On 6 February 2021, judges decided that, despite UK law prohibiting law enforcement agencies from using evidence obtained from interception in criminal trials, communications collected by French and Dutch police from EncroChat using software “implants” were admissible evidence in British courts.
- Belgian police raid 200 premises in drug operation linked to breach of encrypted phone network: On 9 March 2021, Belgian police raided 200 premises after another encrypted phone network with parallels to EncroChat, Sky ECC, was compromised, in what prosecutors described as one of the biggest police operations conducted in the country.
- Arrest warrants issued for Canadians behind Sky ECC cryptophone network used by organised crime: Following the international police operation to penetrate the Sky ECC network and harvest “hundreds of millions” of messages, a federal grand jury in the US indicted Sky Global’s Canadian CEO, Jean-François Eap, along with former phone distributor Thomas Herman, for racketeering and knowingly facilitating the import and distribution of illegal drugs through the sale of encrypted communications devices.
- Judges refuse EncroChat defendants’ appeal to Supreme Court: In early March, judges refused defendants leave to challenge the admissibility in UK courts of message communications collected by French cyber police from the encrypted phone network EncroChat. Computer forensic experts working on EncroChat cases said that decision should trigger a wider review of the “far-reaching effects” the legal decision by the Court of Appeal would have on the role of communications interception in future cases.
- UK courts face evidence ‘black hole’ over police EncroChat mass hacking: Forensic experts say that French investigators have refused to disclose how they downloaded millions of messages from the supposedly secure EncroChat cryptophone network used by organised criminals – leaving UK courts to grapple with a forensic ‘black hole’ of evidence.
- Court hearings precipitated by police cracking the EncroChat secure mobile phone network have been delayed after defence lawyers request further disclosures on police decryption capabilities.







